SS7 — THE DEADLIEST ATTACK
Smartphones have created a revolutionary change in telecommunication and their usability extends way beyond what is expected. A recent report says:
Children spend twice as long on smartphones as talking to their parents.
This is terrible!
Smartphones are used by people for almost every task nowadays. From making online payments to social messaging, e-banking, and even hours of phone calls, we rely heavily on them. However, have you ever stopped for a moment and considered whether the data on your smartphone is really safe and secure?
Nooo! Every data in your Smartphones are vulnerable to Attack!
Your phone number consisting of 10 digits could potentially grant someone unauthorized access to your text messages, phone conversations, and locations without your awareness. This occurrence has happened before and it may or may not happen in the future.
And this Deadliest Attack is called — “The SS7 Hack Attack”
Signaling System 7 (SS7), is a protocol that is used for exchanging data between network devices in worldwide network infrastructure.
Consider you are attempting to make a phone call (from Carrier A) to your friend who is far from(to Carrier B). This is how your voice messages get transmitted to the other end.
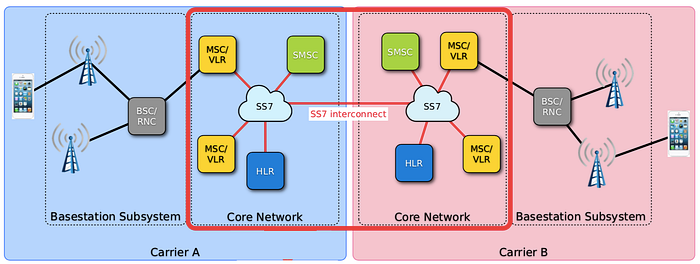
Phone signals are reached by the base stations to nearby towers and transmitted to the SS7 network in carrier A. Every SS7 Network has components such as:
- HLR(Home Location Register): contains a database with subscriber’s information such as phone number, pre-paid contract, call/text data permissions
- VLR(Visitors Location Register): contains a database of the geographical location which are close to the subscriber’s location
These SS7 network devices exchange data from Carrier A to B and vice versa and finally, it successfully reaches the other end of the subscriber.
But, this protocol (SS7) which is used by over 800 global telecoms, is insecure and can be easily compromised by hackers.
No established security system has been deployed in the SS7 network protocol. Once a hacker gets access to the SS7 network, he/she can
- listen and record your phone calls
- read SMS messages that are sent & received
- track geographical locations
They can also easily bypass two-factor authentication which is usually sent via SMS to a user. A hacker who listens to the particular network can intercept that SMS message and exploit the information shared.
How do they Attack?
To attack, You need to dig deeper to find a suitable provider for your network.
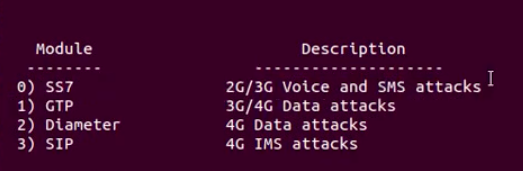
SigPloit, a signaling security testing framework used to exploit vulnerabilites in the signaling protocols
1.1 Installing SigPloit
cd SigPloitsudo pip2 install -r requirements.txtpython sigploit.py
1.2 Selecting the Module as SS7
1.3 Setting the options:
client_pc, serve_pc, client and server IP, port, MSISDN (phone number)

1.4 Capturing packets from any packet analyzer
1.5 Gathering Information using “HackRF one” hardware tool.
Hacking Whatsapp:
Let’s consider the example of Whatsapp, where over 1 billion people in over 180 countries use it daily. Although, the application is End-to-End Encrypted, the account verification for WhatsApp is still done via SMS or Mobile Call. Hackers use this to their advantage and target the SS7 network.
If the hacker has possession of your phone number and can use an SS7 attack to intercept your SMS verification messages, they can effortlessly gain access to your account by associating it with their own WhatsApp account.
How to Survive the SS7 Attack?
Experts suggest implementing a new methodology for the replacement of SS7 networks. But it was said that SS7 Vulnerability is not a Flaw, It was designed that way.
Later, A German cybersecurity researcher came up with an Android application: SnoopSnitch
SnoopSnitch would collect and analyze mobile radio data to make you aware of your mobile network security and to warn you about threats like fake base stations, user tracking, and SS7 attacks.
To install this application, the phone has to be rooted. Root privileges will be needed to collect mobile network data.
Currently, SnoopSnitch is compatible only with Android phones.
These are the web links that describe the incident that happened on the loophole of SS7 networks:
Although, SS7 Attacks cannot be prevented from the attack they can, however, be detected in Network Function Virtualisation using Machine Learning.
Detecting SS7 Attack using ML
This is a research paper contributed by Tooba Qasim & Team, Pakistan.
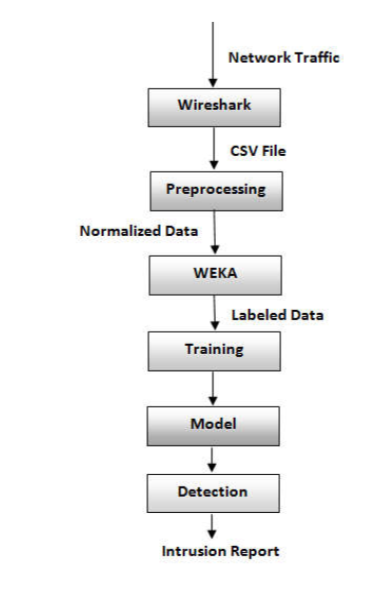
- Their idea was to apply Machine learning to SS7 network data obtained through a packet analyzer
- It is then exported as a CSV file to preprocess the nominal data to a numeric one
- Suitable algorithms were to be chosen, according to the type of data selected. They have used WEKA (a collection of ML algorithms)
- 4 classifiers are used to generate the model and results obtained by each classification algorithm are later analyzed and evaluated.
- The faster algorithm with good results is chosen always.
Conclusion
The research of the 2018 report has shown that the level of security of mobile communication networks is still low. Initially, Many Telecom companies thought the SS7 attack was a low-level risk, but some unknown hackers have already proved them wrong by exploiting its flaws in it. So, It is always advised to stay safe and secure with your digital data.
Within your Google account lies a feature referred to as “Google Activity,” designed to document a comprehensive collection of your internet activity. This includes your browsing history, search histories, physical locations, contact information, and other additional details.
If a hacker tries to retrieve your Google account by using forget password, he/she would be prompted for a 2FA Verification which would be a 6-digit-code that would be sent as SMS. Hackers would easily intercept your SMS by attacking the SS7 Network
அப்பறோம் என்ன
BANG BANG BANG !!
.
.
.
Find me on: Twitter | Github | LinkedIn | Instagram | TryHackMe
